Cogito is a compilation chain that automatically deploys countermeasures against side channel and fault injection attacks to enhance the security of software and data embedded in electronic systems.
Electronic systems like smart cards, IoT devices, and smartphones have embedded software that collects, stores, and processes sensitive data. The kind of software found in embedded systems is particularly vulnerable to side channel and fault injection attacks—two kinds of hardware attack.
Side channel attacks look at the physical behavior of a system, observing things like power consumption at runtime. Fault injection attacks, as the name suggests, introduce glitches into a system in order to change the behavior of the clock or power supply, for instance. The end goal of both of these attacks is to disrupt normal execution of the embedded software to extract secret keys or bypass security mechanisms.
Cogito automatically integrates countermeasures into potentially vulnerable software during the compilation phase, shielding embedded systems against these hardware attacks. Securing software at compile time offers several advantages, including:
Cogito offers a broad and varied range of countermeasures. These include CEA-List software bricks built on techniques patented by the institute. One example is code polymorphism, which intentionally causes software behavior to vary without changing the software’s functional properties, dramatically reducing the effectiveness of attacks.
Cogito uses the LLVM compiler infrastructure.
Cogito is the fruit of research carried out under several collaborative projects funded by the French government and the EU. These include the ANR (French national research agency) Cogito project, which ran from 2013 to 2017.
Cogito’s main advantages:
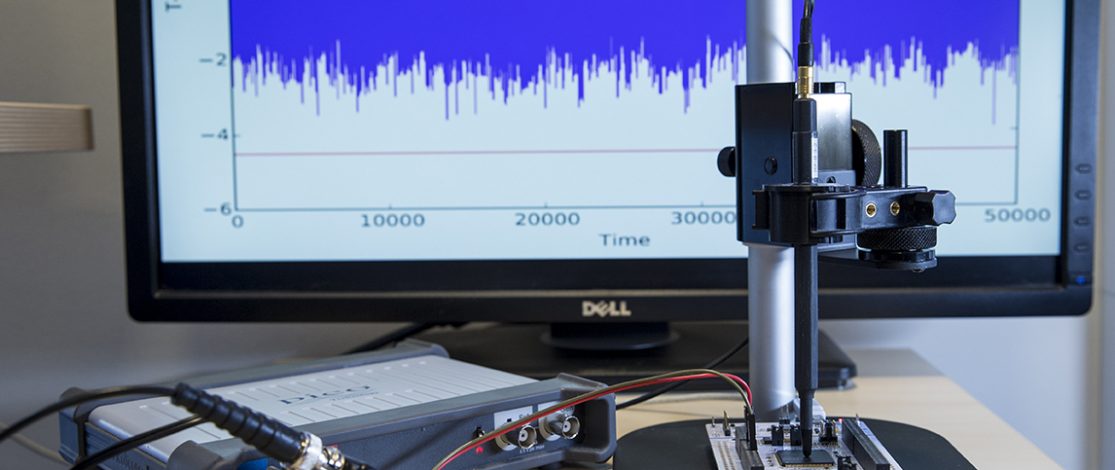
Electromagnetic radiation measurement bench observed with a probe and an oscilloscope. Cogito can help protect this potential channel of attack.
Runtime Code Polymorphism as a Protection against Side Channel Attacks, D. Couroussé, T. Barry, B. Robisson, P. Jaillon, O. Potin, and J.-L. Lanet, in 10th IFIP International Conference on Information Security Theory and Practice (WISTP), 2016.
Compilation of a Countermeasure against Instruction-Skip Fault Attacks, T. Barry, D. Couroussé, and B. Robisson, in Proceedings of the Third Workshop on Cryptography and Security in Computing Systems (CS2), 2016.
Automated Software Protection for the Masses against Side-Channel Attacks, N. Belleville, D. Couroussé, K. Heydemann, and H.-P. Charles, ACM Transactions on Architecture and Code Optimization (TACO), vol. 15, no. 4, 2019.
Maskara: Compilation of a Masking Countermeasure with Optimised Polynomial Interpolation, N. Belleville, D. Couroussé, K. Heydemann, Q. Meunier, and I. Ben El Ouahma. IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems (TCAD), 2020.
PROSECCO: Formally-Proven Secure Compiled Code, N. Belleville, D. Couroussé, E. Encrenaz, K. Heydeman and Q. Meunier, in C&ESAR, 2021.
Code Polymorphism Meets Code Encryption: Confidentiality and Side-Channel Protection of Software Components, L. Morel, D. Couroussé, and T. Hiscock ACM Digital Threats: Research and Practice (DTRAP), 2021.
SCI-FI – Control Signal, Code, and Control Flow Integrity against Fault Injection Attacks, T. Chamelot, D. Couroussé, and K. Heydeman. Design, Automation & Test in Europe Conference (DATE), 2022.